Examples & Guides
Practical implementation patterns, antifraud playbooks, and production-ready integration recipes.
Use this section as a working library: architecture ideas, rollout checklists, and clear examples
for login, signup, checkout, and anti-abuse scenarios.

Learn how to build a practical feedback pipeline for geo anomaly detection in your systems architecture, focusing on incident triage and improved risk decisions.
Read article

Architecting secure and reliable cross-border payout systems requires robust anomaly detection. This guide outlines a zero-trust approach, focusing on identifying and mitigating risks associated with flash sales and regional bot surges in the logistics sector.
Read article
Explore a forward-thinking approach to location anomaly suppression thresholds, optimizing risk control platforms for cross-border merchant onboarding while adhering to strict compliance and audit trail requirements. This article provides a detailed roadmap for achieving better SLA adherence in high-load windows, calibration of thresholds, and data enrichment techniques.
Read article
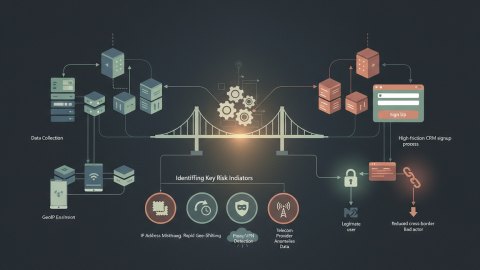
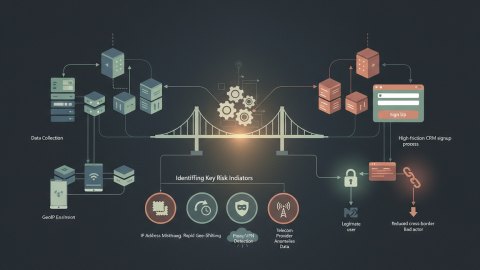
Learn how to implement risk scoring for roaming mobile IP addresses in a high-friction CRM signup process, improving conversion rates and reducing cross-border abuse. A practical guide for personal systems architects.
Read article

Improve payment gateway resilience by simulating region-specific traffic anomalies. This guide details architecture decisions, replay strategies, and validation techniques for robust payment processing, focusing on identifying and mitigating vulnerabilities before they impact live transactions.
Read article

Explore the architecture of geo-informed zero trust access for enhanced security posture. Learn how to integrate geolocation data precisely into your identity and access management (IAM) systems to create a dynamic, context-aware authorization process. This guide details the technical strategy, API considerations, and implementation blueprints for a B2B environment, particularly focused on real-time risk decisioning.
Read article

Learn how to architect a system for country-based risk throttling in your APIs while prioritizing user privacy. Explore techniques, from signal gathering to monitoring, to mitigate abuse without compromising user data.
Read article

Enhance the reliability of webhook-based geo enrichment in logistics payout systems with a practical trust benchmarking checklist. Discover how to mitigate policy drift and signal loss during cross-border onboarding validations, and measure ROI.
Read article

Implement privacy-respecting geo-aware device binding in zero-trust marketplaces to detect regional fraud rings and increase confidence in payout SLAs. This guide provides a C-level overview of architectures and implementation strategies, prioritizing user privacy and minimizing data collection.
Read article
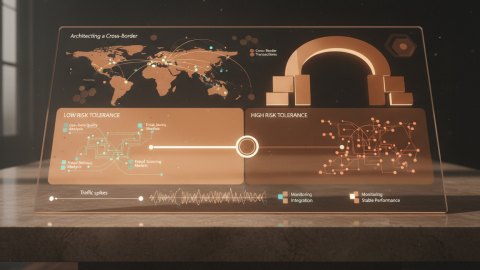
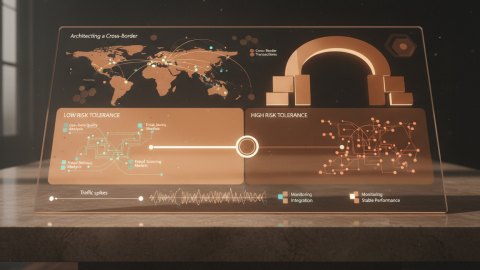
Design and implement a robust Cross-Border Fraud Exposure Index (CBFEI) to mitigate payout fraud in global logistics operations. Learn how to analyze geo-data quality, build a risk scoring model, and integrate monitoring to ensure stable performance under traffic spikes.
Read article